How to access, set up, and test your account
Mailing lists and communication with admins and other users
-
cms-tier3-users@lists.psi.ch: list through which we broadcast information (e.g about downtimes). It can also be used for discussions among users (e.g. getting help from other users). You must subscribe to this list using its web interface (list archives
(list archives ).
).
-
cms-tier3@lists.psi.ch: Use this list to reach the Tier-3 admins, typically if you have a problem and you need help. What you write to this list is only seen by the administrators
Both lists are read by the administrators and are archived.
First Steps on T3 User Interfaces (UI)
Three identical User Interface servers ( UIs ) are available as login nodes for the Tier-3 cluster. You can test your programs there, submit batch jobs and do some interactive work. But production runs that inflict a heavy load on the system are not permitted, since they willl impact the work of other users. Please run such jobs in the batch queues (one can also run interactively in an allocated batch slot).
Access to Login nodes is based on the institution
The access is not restricted to allow for some freedom, but you are requested to use the UI dedicated to your institution.
| UI Login node |
for institution |
HW specs |
| t3ui01.psi.ch |
ETHZ, PSI |
132GB RAM , 72 CPUs core (HT), 5TB /scratch |
| t3ui02.psi.ch |
All |
132GB RAM , 72 CPUs core (HT), 5TB /scratch |
| t3ui03.psi.ch |
UNIZ |
132GB RAM , 72 CPUs core (HT), 5TB /scratch |
- Use
ssh to log in to a UI server t3ui0* server. You can use -Y or -X flag if you want to work with graphical X applications.
ssh -Y YourUsername@t3ui02.psi.ch
- If you are an ETHZ or UniZ user and do not have a regular PSI account, you will have to change your initial password after logging in for the first time. Modify the initial password by using the
passwd command.
- Check that you can access the Storage Element through the NFS protocol, by just creating and deleting a test file in your user area
touch /pnfs/psi.ch/cms/trivcat/store/user/${USER}/my-first-test
rm /pnfs/psi.ch/cms/trivcat/store/user/${USER}/my-first-test
- Check that you can access the NFS /work area
touch /work/${USER}/my-first-test
rm /work/${USER}/my-first-test
- For setting up the basics for the CMS software environment, make sure that this works for you
source ${VO_CMS_SW_DIR}/cmsset_default.sh
Access to the SE (Storage Element) - requires Grid Certificate
The following tests only apply if you own a
Grid certificate for authentication on the LHC Grid, and if you registered that certificate with us in your account application. Also, you should register in the
chcms VOMS group in order to get access to certain services of the Swiss Tier-2 center (see below).
- In order to work with resources on the WLCG grid you need to have a grid x509 certificate and a matching private key. Copy these credentials to the standard locations of
~/.globus/userkey.pem and ~/.globus/usercert.pem on one of the T3 user interface hosts and make sure that their permissions are properly set. The user key must NEVER be readable by any other user!
chmod 600 userkey.pem
chmod 644 usercert.pem
For details about how to extract those .pem files from your CERN User Grid-Certificate ( usually a password protected .p12 file ) please follow https://twiki.cern.ch/twiki/bin/view/CMSPublic/PersonalCertificate .
.
- Make sure that your credentials are registered with the CMS Virtual Organization CERN details about that
 . Else, the next step will fail.
. Else, the next step will fail.
- Create you short term credentials in the form of a proxy certificate with CMS extensions (valid for 168 hours):
voms-proxy-init -voms cms --valid 168:00
If the command fails you can run it again adding a -debug flag to troubleshoot the problem.
- Test your access to the PSI Storage element using our
test-dCacheProtocols testing suite
$ test-dCacheProtocols
[feichtinger@t3ui01 ~]$ ./test-dCacheProtocols
TEST: GFTP-write ...... [OK]
TEST: GFTP-ls ...... [OK]
TEST: GFTP-read ...... [OK]
TEST: DCAP-read ...... [OK]
TEST: XROOTD-LAN-write ...... [OK]
TEST: XROOTD-LAN-stat ...... [OK]
TEST: XROOTD-LAN-read ...... [OK]
TEST: XROOTD-LAN-rm ...... [OK]
TEST: XROOTD-WAN-write ...... [OK]
TEST: XROOTD-WAN-read ...... [OK]
TEST: XROOTD-WAN-rm ...... [OK]
TEST: SRMv2-write ...... [OK]
TEST: SRMv2-ls ...... [OK]
TEST: SRMv2-read ...... [OK]
TEST: SRMv2-rm ...... [OK]
- If a test fails, an error message will be written to the screen, and it will point you to a file containing the details of the error. Please send this together with all the information to cms-tier3@lists.psi.ch.
- TIP: You can use the
-v (verbose) flag to see the commands that the script executes. This is a good way to learn about the slightly esoteric syntax for interacting with grid storage. If you supply a -d flag as well, the tests will not be run, but you will be able to look at all the actions that the script would execute.
- Test write access to your user area on the storage element. The user area is located underneath
/pnfs/psi.ch/cms/trivcat/store/user and has by convention your cms hypernews name name as directory name. However, due to historic procedures, it might also be that your Tier-3 login name is used for this directory /pnfs/psi.ch/cms/trivcat/store/user/${your_cms_name}. E.g.
test-dCacheProtocols -l /pnfs/psi.ch/cms/trivcat/store/user/feichtinger
TEST: GFTP-write ...... [OK]
TEST: GFTP-ls ...... [OK]
TEST: GFTP-read ...... [OK]
TEST: DCAP-read ...... [OK]
TEST: XROOTD-LAN-write ...... [OK]
TEST: XROOTD-LAN-stat ...... [OK]
TEST: XROOTD-LAN-read ...... [OK]
TEST: XROOTD-LAN-rm ...... [OK]
TEST: XROOTD-WAN-write ...... [OK]
TEST: XROOTD-WAN-read ...... [OK]
TEST: XROOTD-WAN-rm ...... [OK]
TEST: SRMv2-write ...... [OK]
TEST: SRMv2-ls ...... [OK]
TEST: SRMv2-read ...... [OK]
TEST: SRMv2-rm ...... [OK]
You may want to read about the
Tier3Storage next!
T3 policies
Please read and take note of our
Policies
Linux groups (partially OBSOLETE - needs to be revised)
Each T3 user belongs to both a primary group and a common secondary group
cms, the former is meant to classify common files like the ones downloaded by the
PhEDEx
file transfer service. T3 primary groups are :
| ETHZ |
UniZ |
PSI |
ethz-ecal |
uniz-higgs |
psi-bphys |
ethz-bphys |
uniz-pixel |
psi-pixel |
ethz-ewk |
uniz-bphys |
|
ethz-higgs |
|
|
ethz-susy |
|
|
For instance this is the
primary and the
secondary group of a generic T3 account :
$ id auser
uid=571(auser) gid=532(ethz-higgs) groups=532(ethz-higgs),500(cms)
The T3 groups areas:
/pnfs/psi.ch/cms/trivcat/store/t3groups
Applying for the VOMS Group /cms/chcms membership to identify as a Swiss CMS user
VOMS is the Virtual Organisation Managent System that is used to manage the CMS groups and roles. Users are identified by their grid certificate.
We manage the 'Swiss' VOMS Group
/cms/chcms. If you run with these added credentials, you can get additional benefits when running on our national Tier-2
T2_CH_CSCS
- write access to directories under /store/user and /store/group. This area is reserved for associated users. All others need to place files in /store/temp/user where they get cleaned regularly.
- currently not active, but we can activate in need
- higher priority on the T2_CH_CSCS batch queues
- additional Jobs slots on the T2_CH_CSCS batch queues
To request membership in our VOMS group
- visit the CMS VOMS page at https://voms2.cern.ch:8443/voms/cms/user/home.action

- You must have your grid certificate loaded in your browser, otherwise VOMS cannot recognize you!
- The page should display information about your VOMS entry, your certificate information.
- Request membership in /cms/chcms
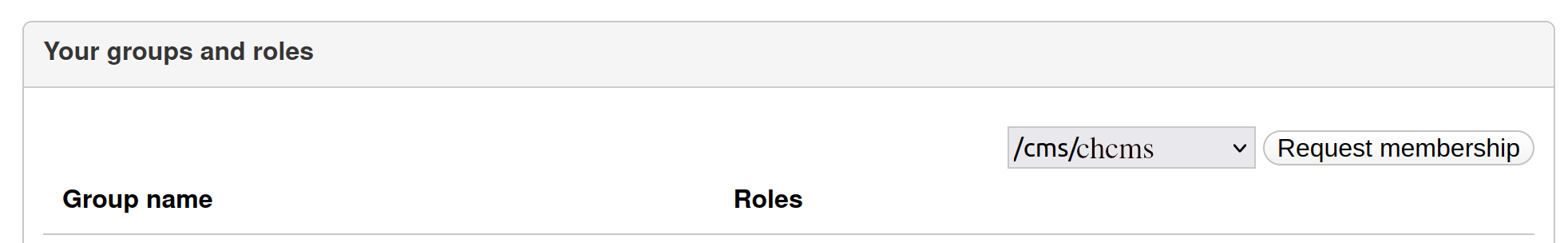
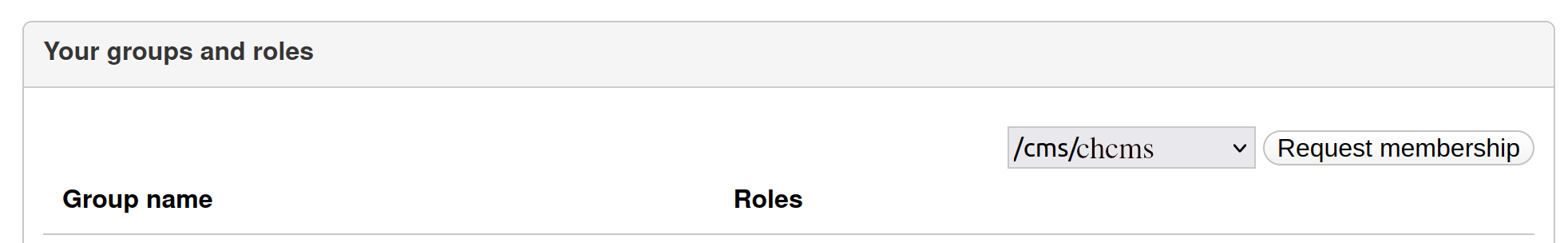
- Scroll down to the section "Your groups and roles" (notice that these boxes can be collapsed/expanded by clicking on the header line)
- In the list box next to the "Request Membership" button, select the
/cms/chcms group, and click the button.
- Allow for 1 day for getting approval.
Creating a valid proxy certificate with the right chcms attributes
Once you get the confirmation for your chcms membership, you can progress to creating chcms proxy certificates. In order to get correctly mapped to a Swiss user account at our Tier-2, you need to create your proxy certificate using a
-voms flag similar to this
voms-proxy-init -voms cms:/cms/chcms
You can confirm your VOMS attributes by running
voms-proxy-info -all
subject : /DC=ch/DC=cern/OU=Organic Units/OU=Users/CN=dfeich/CN=613756/CN=Derek Feichtinger/CN=1404297260
issuer : /DC=ch/DC=cern/OU=Organic Units/OU=Users/CN=dfeich/CN=613756/CN=Derek Feichtinger
identity : /DC=ch/DC=cern/OU=Organic Units/OU=Users/CN=dfeich/CN=613756/CN=Derek Feichtinger
type : RFC3820 compliant impersonation proxy
strength : 2048
path : /t3home/feichtinger/.x509up_u3896
timeleft : 191:59:42
key usage : Digital Signature, Key Encipherment
=== VO cms extension information ===
VO : cms
subject : /DC=ch/DC=cern/OU=Organic Units/OU=Users/CN=dfeich/CN=613756/CN=Derek Feichtinger
issuer : /DC=ch/DC=cern/OU=computers/CN=cms-auth.web.cern.ch
attribute : /cms/chcms/Role=NULL/Capability=NULL
attribute : /cms/Role=NULL/Capability=NULL
timeleft : 24:59:41
uri : voms-cms-auth.app.cern.ch:15000
Make sure that the chcms attribute
/cms/chcms/Role=NULL/Capability=NULL appears before the attribute for the standard CMS membership
/cms/Role=NULL/Capability=NULL in that listing!
Your chcms prioritzed proxy certificate will be accepted as a normal CMS proxy certificate when accessing other sites (since it also includes the normal /cms group).
Note that it is possible to ask for multiple attributes and roles with a single
voms-proxy-init command! The order of resulting attributes will reflect the order you gave on the command line, and our grid site will map you with the first attribute that matches on of our rules. So, e.g. if you had created your proxy by
voms-proxy-init -voms cms:/cms -voms cms:/cms/chcms, then the mapping to a normal CMS user without special rights would take precedence.
Testing write access to T2_CH_CSCS as a Swiss user
Having created your grid proxy with the correct
chcms attribute, as described above, execute the following line from one of our Tier-3 login nodes. ${USER} should be your CMS name (usually the CERN login name also used on lxplus)!
gfal-copy file:///t3home/T3-INFO/USER-SPACE-ACCOUNTING \
root://storage01.lcg.cscs.ch:1096/pnfs/lcg.cscs.ch/cms/trivcat/store/chcms-user-test/test-${USER}
If you get a permission denied error, try to test whether you are allowed to write to the space open for writing to all CMS users
gfal-copy file:///t3home/T3-INFO/USER-SPACE-ACCOUNTING \
root://storage01.lcg.cscs.ch:1096/pnfs/lcg.cscs.ch/cms/trivcat/store/temp/user/test-${USER}
If only the latter test succeeds, there is still a problem with your chcms membership or the mapping. Please contact us on the admin mailing list.
Optional Initial Setups (partially obsolete)
Installing the CERN CA files into your Web Browser
In dealing with grid sites, or for having your own certificate accepted inside of your browser, you may need to add the CERN CA (certificate agency) records to the default ones present in your browser. You can obtain them from
CERN CA file
.
 (list archives
(list archives ).
).
 .
.
 . Else, the next step will fail.
. Else, the next step will fail.